Whether you are setting up a business network, planning on buying a new computer, or want to protect your home computer from hackers, it’s important to understand how security networking works. It’s not easy to find out, but it can be a crucial step in your quest to keep your personal information safe. Here are some of the things you need to know.
Intrusion prevention system (IPS)
IPS is a form of security that monitors network traffic and detects anomalies. It is designed to block threats automatically. It can also detect malware and other malicious patterns, preventing denial of service attacks and brute force attacks.
A sound IPS system can act independently or be linked with other security controls must-have NGFW features. In addition to detecting threats, the system can perform other tasks, such as correcting cyclic redundancy check errors and removing unwanted transport layer options.
An IPS can be configured with customized security policies that control traffic in specific ways. For example, a network can be configured to use a special URL filtering technique. This will allow connections to be made without interference from other network traffic. It is also possible to have an IPS perform its functions as a host device rather than a firewall.
An intrusion detection system (IDS) is a similar tool. It monitors network traffic and sends alerts to a designated administrator. It is a software tool that works within an enterprise network. The main difference between an IDS and an IPS is the type of information it can detect.
The IDS is an excellent tool for finding the most critical security measures, but it is not a complete solution. For example, some vendors provide a multi-category IDS that includes signature-based and anomaly-based detection.
Mobile device security
Investing in effective mobile device security solutions is important in protecting your company’s data. However, while mobile devices offer a variety of benefits, they also present several risks.
One of the most prominent is the risk posed by malicious apps. These apps provide a gateway for hackers to access your corporate network. In addition, they can be downloaded from third-party sources and masquerade as legitimate software.
The best way to detect these malware-ridden applications is to perform on-demand scanning. This type of scan runs in the background and provides detailed scan results. Aside from protecting against malware, it can also prevent calls to unidentified numbers and prevent sending SMS messages.
Another security solution is the use of a virtual workspace. This is a web-based environment that employees or visitors can access to provide a secure place to conduct business. This virtual space can be single-user, multiple-user, or corporate-owned. In addition, it can contain all of your corporate applications and data, giving you real-time visibility into your mobile risk.
The NIST Cybersecurity Practice Guide addresses the challenge of securely deploying and managing mobile devices in the enterprise. This includes a suite of tools that can be implemented in parts or whole.
While the best way to secure your devices may be a mixture of technologies, each part of the technology stack has inherent risks.
Web security
Using security networking to protect the web has become a priority. It is critical to the operations of any organization. The number of websites has exploded, with more than 1.7 billion expected by 2020. In addition, web applications are now the primary target of cybercriminals. These hackers aim to steal data to access payment systems and email accounts.
For instance, attackers often use malicious scripts called cross-site scripting to pretend to be another user and access crucial data. This can happen when the user inputs an unprotected field or refers to external scripts. In many cases, these attackers have downloaded malware to the targeted website.
Hackers can also use malware to spy on users, intercept email messages, and exfiltrate data. Additionally, hackers can use known-bad URLs to access critical information.
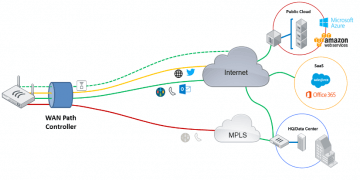
As more and more organizations migrate to web-based infrastructures, web security is becoming a critical component of business continuity. A secure web gateway provides threat protection, blocking unwanted traffic and preventing malware infections. These solutions also allow for policy enforcement. These technologies can provide a comprehensive web security solution combined with content inspection.
These solutions offer deep visibility into all web traffic, including those originating at the application layer. This granular visibility allows web administrators to define rules specific to each application. They can also inspect all traffic for actions that violate corporate policies.
Phishing attacks
Using a security networking approach is a powerful way to prevent phishing attacks. It’s a multi-layered approach based on technological, process and people-based approaches. Each layer should be addressed as part of a comprehensive mitigation strategy.
One of the most common tactics cybercriminals use to steal valuable data is phishing. This social engineering attack targets a specific person or group and tries to coerce them into clicking on a bogus link or attachment. The attack often involves a branded message from a trusted source.
The key to preventing phishing is educating staff about what to look for and ensuring everyone is aware of the attack. You’ll also want to provide them with a process for reporting suspicious emails.
Some of the best ways to prevent phishing are to use a spam filter, change your passwords frequently, and have two-factor authentication. These measures will prevent hackers from gaining access to your systems and will give your organization the ability to restore data and protect against further attacks.