Identity governance is a security discipline focusing on user access management and regulatory compliance. It enables organizations to reduce security risks and maintain compliance by allowing only authorized users to access information and applications.
Identity governance solutions provide centralized visibility into identities and access privileges. They help detect inappropriate access, policy violations, and weak controls.
Security
Identity Governance and Administration emerged as more users needed access to organizational resources from more devices and locations. As more devices were connected to the Internet, security risks increased. IGA is automating and securing identities across user accounts, roles, and entitlements to provide more control over access to technology assets and mitigate risk.
For example, identity governance and administration solutions streamline the provisioning of user access reducing the time and cost of help desk requests. It also provides automated policy enforcement to ensure compliance with business and IT policies and regulatory requirements.
Today’s comprehensive identity governance solutions offer more sophisticated and effective features, including role-based authentication and centralized policy management. They also use artificial intelligence to analyze patterns and flag potential discrepancies.
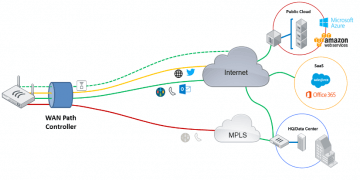
The best IGA solutions integrate with directories and other enterprise systems containing information about users, their applications, and the resources they access. They also work with Identity and Access Management (IAM) processes to automate workflows that streamline the entire access lifecycle, from onboarding and offboarding to bulk approvals.
Ideally, IGA is a core component of an overall identity strategy that includes onboarding and offboarding, provisioning, and policy management. It can help businesses secure their digital identities and minimize the risk of cyberattacks while empowering employees to be productive no matter where or what device they use.
Compliance
Identity governance and administration (IGA) uses policies and processes to manage identities and access rights. These policies can be applied to various organizational areas, including security, business processes, and technology.
IGA helps organizations control user access to information and systems, reducing risk while meeting compliance requirements. This is especially important in industries where there is a need to meet regulatory requirements. For example, government regulators in certain sectors require organizations to abide by specific privacy or financial data regulations. The use of a centralized identity management platform is key to this process. These solutions can automate some functions, such as account and credential administration, user and device provisioning and de-provisioning, entitlement management, access reviews, analytics, and reporting.
Efficiency
Managing identity and access is challenging as organizations become more digital and their user base grows. Excessive or inappropriate user access can pose a security threat and make an organization more susceptible to data breaches.
Identity governance and administration solutions help organizations manage user access and ensure compliance while reducing operational inefficiencies. They also improve employee productivity and security by providing access to the right resources at the right time.
Effective identity governance and administration requires a combination of policies, processes, and controls. These can include segregation of duties, a principle of least privilege that allows identities only to access the devices, servers, and applications they need for their jobs.
These processes can be automated or rolled out as changes occur in the business environment and technologies. They can also be backed by reporting, analytics, and other tools that improve visibility into security and compliance.
Many IGA products are designed to be cloud-based and integrate with existing IT systems. This lets businesses easily move their systems and data into the cloud while maintaining compliance.
Some IGA products can be integrated with other identity management technologies to create a complete enterprise-class solution. This helps organizations secure sensitive information, meet regulatory requirements, and automate identity-related security processes without requiring major IT resources.
IGA programs must be monitored to ensure they achieve the desired results and perform as planned. This requires a continuous reassessment of implementation and improvements in analytics and reporting.
For example, if a business’s identity governance program isn’t fully meeting new privacy mandates or the needs of a specific industry, it might need to be adjusted to accommodate them.
Cost
Identity governance and administration (IGA) are essential to your security strategy. It helps you meet regulatory requirements and maintain data privacy. It also automates processes and policies that help you manage access to sensitive information, secure devices, and protect business-critical systems and applications.
As digitization continues to change the way businesses do business, organizations must be able to manage identities and access them efficiently. With this, organizations can avoid the cost and disruption of data breaches or cybersecurity attacks.
Managing identity governance and administration is critical for companies in highly regulated industries, such as financial services and health care. Regulations like GDPR, SOX, and HIPAA place high expectations on data privacy and require that organizations have an effective IGA solution to meet these standards.
A good IGA solution automates and streamlines access certifications, access requests, password management, and provisioning. This reduces operational costs and frees IT staff to focus on more strategic matters.
Another key function is identity analytics, which detects suspicious activity and prevents unauthorized access to sensitive information. This technology leverages machine learning algorithms to identify and monitor privileged accounts and their entitlements for access.
The process can help to detect threats and speed up response times, saving your company the expense of a data breach. It also gives you a clear view of your user population and enables you to make more informed decisions about the right people and technologies to support your business goals.